Cloning Methodologies
An authoritative examination of bit-perfect macOS volume replication. We explore the architectural shift from simple file copying to block-level synchronization within the Apple File System (APFS).
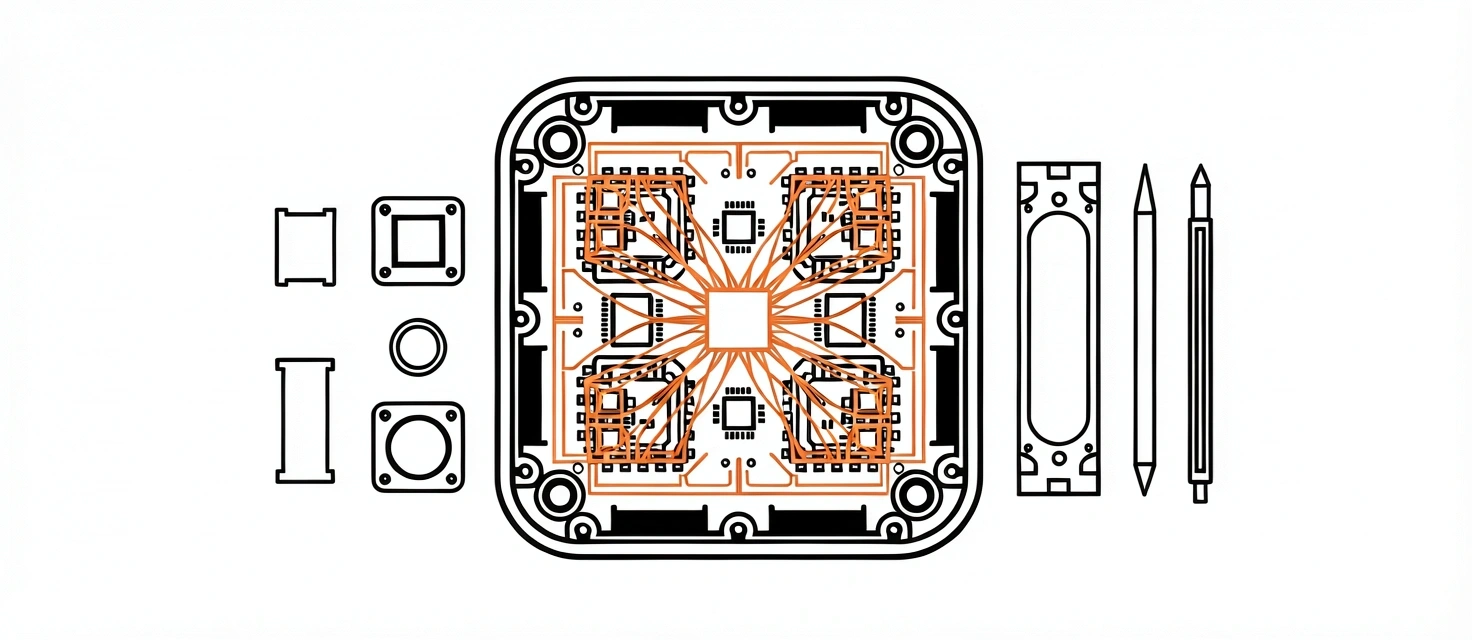
The Block-Level Foundation
In a mac disk clone scenario, the objective isn't merely to move files, but to mirror the underlying physical storage geometry.
File-Based vs. Block-Based Replication
Traditional backups operate at the file level. The OS queries the file system, reads individual items, and writes them to a new destination. This process is susceptible to metadata loss and ignores the structural complexity of APFS.
A true mac clone using block-level methodology bypasses the file system abstraction. It copies segments of data directly from the SSD controller, replicating the exact bit-state of the source. This ensures that hidden system structures—including symlinks, hard links, and extended attributes—remain intact.
- Ignores Disk Permissions
- Skips Hidden System Folders
- Destroys APFS Snapshots
- Captures APFS Inodes
- Preserves Container Layout
- Bit-Perfect Recovery Volume
Infrastructure Requirements
Selecting the correct medium when you clone mac to ssd is the difference between an archival artifact and a functioning disaster recovery system.

Thunderbolt Hub Standard
The Apple T2/M-Series Barrier
Modern hardware utilizes the Secure Enclave to manage boot volume ownership. A simple copy fails because the hardware requires a cryptographically paired Preboot partition. Our methodologies focus on ensuring these secondary partitions are properly synced to the external media.
CRC Verification Passes
Speed is a secondary metric; integrity is primary. Utilizing a ccc backup mac strategy allows for post-cloning verification. This involves checking cyclic redundancy check (CRC) values on the source and destination to ensure no silent bit-flip occurred during the transfer.
Architecture: Intel vs. Apple Silicon
The evolution of the "Signed System Volume" (SSV) requires separate handling for the System and Data volumes.
Unrestricted Volume Replication
Intel-based hardware allows for a unified cloning process. The entire APFS container, including the macOS System volume and the Data volume, can be moved as a single entity. External booting is managed via the Boot Picker (Option key at startup) without significant internal security handshakes.
Signed System Volume (SSV) Support
Apple Silicon requires a bifurcated mac disk clone strategy. Because the System volume is cryptographically sealed and read-only, methodologies now prioritize cloning the "Data" volume. To make this bootable, a clean OS is installed on the target, followed by a block-level transplant of the user Data volume.
The Fallacy of the Successful Finish
A progress bar reaching 100% does not signal a valid backup. Without a secondary bit-for-bit checksum verification, you are operating on hope, not engineering. Our recommended methodology mandates a post-write scan where every block is re-read and hashed against the source. If even a single bit deviates, the clone is considered failed.
We utilize APFS snapshots to ensure the source is 'frozen' in time, preventing changes during the copy process.
Open system files are replicated using secondary shadow services, ensuring no 'file-in-use' errors occur.
User Identification (UID) and permissions are mapped 1:1, guaranteeing immediate access post-migration.
Note on Modern Security Features
The integrity of your mac disk clone is intrinsically linked to the Secure Enclave. When moving data to a new SSD, you must manually authorize the external medium within the "Startup Security Utility" found in Recovery Mode. Without this hardware-level handshake, even a bit-perfect clone will be rejected by the system's root of trust.
Methodology Comparison Matrix
| Criterion | Block-Level (Method A) | File-Based (Method B) | Snap-Sync (Method C) |
|---|---|---|---|
| Integrity Depth | Absolute (All data layers) | Selective (Files only) | Temporal (State-based) |
| Boot Potential | 100% (High Confidence) | 0% (Manual rebuilding req.) | 85% (Requires Preboot sync) |
| Speed Coefficient | Hardware Bound (Max SSD) | Metadata Bound (Latency) | Incremental (Optimized) |
| Recommended For | Disaster Recovery | Simple Folder Transfers | Daily Differential Backup |